Webhook And Event Catalog
Outbound webhook configuration, delivery headers, signature model, current event types, and notification streaming
Ask AI about this page
Get answers grounded in the live Obelisk docs set, with source links, selected-text explainers, and prompts for the next document to read.
This page documents the event surfaces that currently exist for organization-facing integrations.
Current Event Surfaces
There are two operator-facing event surfaces today:
- outbound webhooks configured per organization
- authenticated server-sent events for organization notifications
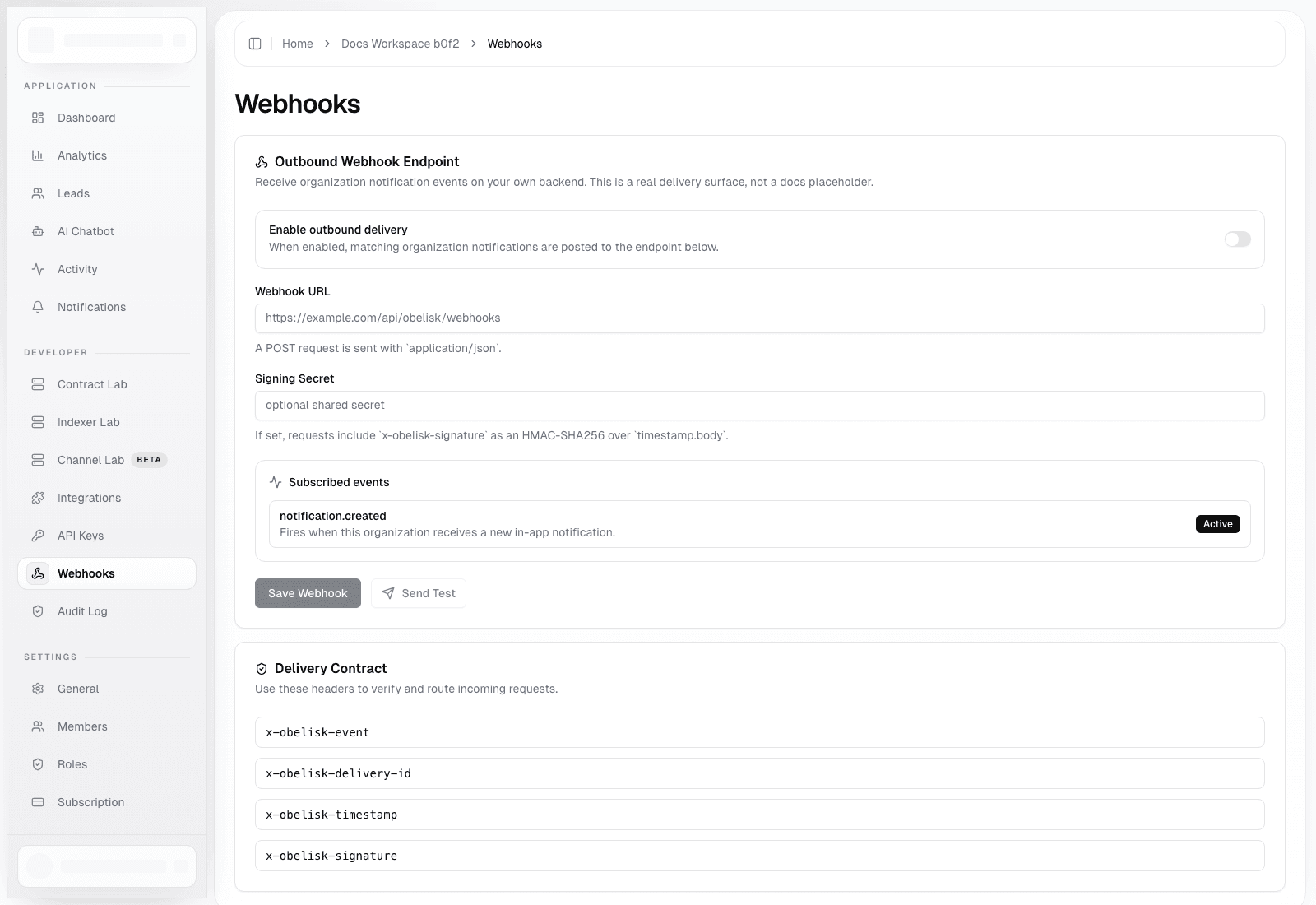
Outbound Webhook Configuration
Configuration fields:
| Field | Type | Notes |
|---|---|---|
enabled | boolean | turns delivery on or off |
url | string or null | required when delivery is enabled |
signingSecret | string or null | optional HMAC secret |
events | string[] | currently supports notification.created |
lastDelivery | object or null | persisted delivery result snapshot |
Only organization owner and admin members can change this config or send a test event.
Current Webhook Event Catalog
notification.created
Emitted when an organization notification is created and outbound delivery is enabled for that event.
Payload shape:
{
"id": "delivery-uuid",
"type": "notification.created",
"createdAt": "2026-03-12T10:00:00.000Z",
"test": false,
"organization": {
"id": "organization-uuid",
"name": "Acme"
},
"data": {
"notification": {
"id": "notification-uuid",
"title": "Title",
"message": "Message",
"level": "info",
"createdAt": "2026-03-12T10:00:00.000Z",
"expiresAt": null,
"metadata": {
"source": "example"
}
}
}
}Delivery Contract
Webhook delivery behavior:
- method:
POST - content type:
application/json - timeout:
5seconds - user agent:
Obelisk-Webhooks/1.0
Headers:
x-obelisk-eventx-obelisk-delivery-idx-obelisk-timestampx-obelisk-signaturewhen a signing secret exists
Signature Model
When signingSecret is configured, the signature is:
HMAC_SHA256(secret, `${timestamp}.${body}`)Validation guidance:
- read
x-obelisk-timestamp - rebuild the exact JSON body string
- compute the HMAC
- compare in constant time
- reject stale or replayed deliveries using
x-obelisk-delivery-id
Test Delivery
The test action sends a synthetic notification.created payload with:
test: true- a generated notification title and message
- sample metadata showing
source: webhook-test
The result is persisted into lastDelivery in organization metadata.
Failure Behavior
If delivery is disabled or the URL is missing, the recorded delivery result is marked unsuccessful.
If the receiver returns a non-2xx response, the failure message stores the HTTP status and response excerpt.
Notification Stream (SSE)
Authenticated operators can also subscribe to:
GET /api/organization/notifications/stream
Current behavior:
- requires a valid signed-in session
- requires
activeOrganizationIdin session - verifies the user is a member of the active organization
- sends
connectedandupdateevents - polls for snapshot changes every
2.5seconds - emits keepalives every
15seconds - rotates the stream around
55seconds to avoid network idle timeouts
SSE Event Names
connectedupdate
The stream is intended for operator-facing clients, not anonymous consumers.
When To Use Which Surface
| Need | Recommended surface |
|---|---|
| push accepted notifications into an external system | outbound webhook |
| update an authenticated operator UI in real time | SSE notification stream |
| automate deployments | public deployment API, not webhooks |